The average internet user barely understands what the actual nuts and bolts of the world wide web are. Ignorance may be bliss but not so for internet users. The misuse of personal data has quickly become a thorny issue for users and businesses that thrive online.
Free access to data enables a free, fast, and relevant internet experience. It, however, encourages vices like identity theft and data security breaches. In a post, Snowden, age, data privacy, and protection has become more critical for individuals and businesses, data analysis, use, and trade comes under increased scrutiny.

Consequently, internet users have quickly adopted privacy tools, private search engines, and adblockers to enhance online privacy. One easy to use privacy tool is the proxy server.
Read Also:
Contents
What is a Proxy Server?
Proxy servers, referred to as proxies, are applications of computers that act as intermediaries between the World Wide Web and your browser. In the absence of a proxy, your request to access your Twitter handle, for instance, goes through a firewall, which allows Twitter access to information such as your IP address.
To deny Twitter this personal information, you can have a proxy server, acting as a gateway between your browser and the website. Consequently, the proxy server will deny Twitter access to your IP address and display its own instead.
Proxy servers are a critical data security component for businesses because they enhance the security of data networks and increase anonymity for the users. Many companies have recognized the need to improve data security by setting up firewalls, using multifactor identification, and inventing in robust anti-malware software.
Read Also:
They can enhance your cybersecurity policy by veiling the IP addresses of your business’s computers to ensure that your data, such as location, ISP, street, or zip code, are kept hidden when online. This can keep crafty cybercriminals away from your business data.
In addition, proxy servers enhance page load times and allow the viewing of restricted or geo-blocked online content. Most important is that they can filter and block access to dangerous websites eliminating the dangers of phishing and malware installations. Some businesses also use this useful function to control internet usage amongst employees while at work.
What are the Different Types of Proxy Servers
There are two major types of proxy servers; the data center and residential proxy server. The main difference between them is that while an ISP provides residential proxies, third parties offer data center proxies. Let us delve into what details below.
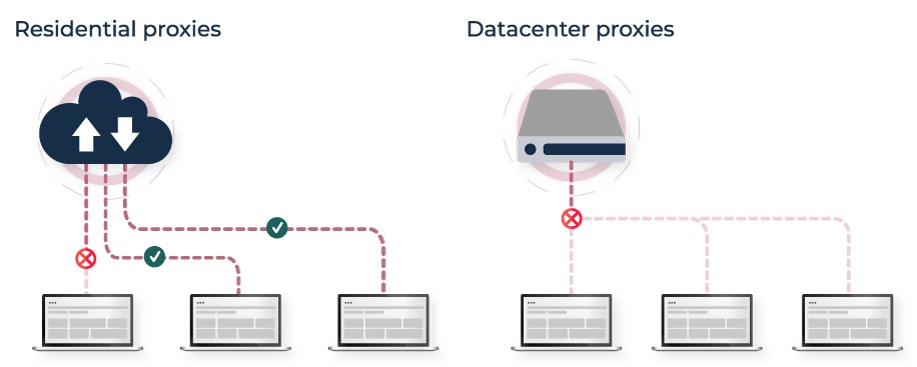
1. Datacenter Proxies
As mentioned, a data center proxy comes from secondary sources and utilize numbers to enhance online anonymity. They are not associated with internet service providers and only provide internet gateways as well as SEO and scraping data services. They offer high speeds of connectivity and are perfect web monitoring tools.
Their main advantage is that they allow businesses unlimited accounts, which can be used in the creation of multiple accounts on a single IP address. Consequently, you can purchase data center proxies in bulk so that you can have a wide array of IP addresses. Datacenter proxies are more affordable than the residential type and are easily accessible.
2. Residential Proxies
A residential proxy server is provided by an ISP and therefore consists of a valid IP address. It is wired directly to your facility, where it masks your current IP address assigning you a different address. The main advantage of a residential proxy server is that e it has an actual physical location. It is, therefore, less likely to be blacklisted by websites.
A residential proxy is perfect for businesses that require web scraping, market research, ad verification, travel fare aggregation, and pricing intelligence services. If you need top-notch web scraping reliability, anonymity, and security for your business, then residential proxies are the way to go. Read more on the web to learn everything there is to know about residential proxies.
Free vs. Paid Proxy?
Today, you will find a lot of ‘free’ proxies on the search for anonymity. These proxies are great for online activity such as web scraping, where you do not need to input any sensitive personal information. Free proxies are perfect for hiding IP addresses.
1. Keep in mind that if you are not paying for the service, you are most probably the product, not the customer. Free proxies can have many huge downsides that include;
2. Tons of server ads and altered websites.
3. Unreliability of server due to high traffic loads which leads to inconsistency and burnouts.
4. The stigma of using proxies that are in many instances used for a nefarious activity such as DDoS attacks, leading to proxy IP address blacklisting.
5. The danger that the free proxy has been set up by a malicious actor awaiting data such as credit card numbers.
6. Identify theft.
7. Exposure to malware from servers that not invested in robust security.
8. The probability that the log records of your internet activity are used to keep tabs on your online activity.
Criteria for Choosing a Proxy Provider
1. Purchase proxies from a business that is highly reviewed and that has an active media profile. A legal entity will be more responsible with your data due to the legal repercussions of failure.
2. Buy proxies and avoid freebies to avoid scammers.
3. Use a proxy provider with an extensive IP pool to enhance targeting.
4. Avoid shared proxies by paying for dedicated or semi-dedicated proxies. Dirt-cheap proxies might offer unlimited traffic but will be unstable and slow.
Read Also:
Conclusion
A proxy server is critical to data security, and an excellent one does not need to put a dent in your business’s pockets. You can have the best of both worlds by accessing reliable proxy server services from recognized providers, which will keep your company’s data access and security policy in top form.